You May Also Enjoy
[CVE-2021-3156] Exploiting Sudo heap overflow on Debian 10 by D3v17
Recently the Qualys Research Team did an amazing job discovering a Heap overflow vulnerability in Sudo. In the next sections, we will analyze the bug and we will write an exploit to gain root privileges on Debain 10.
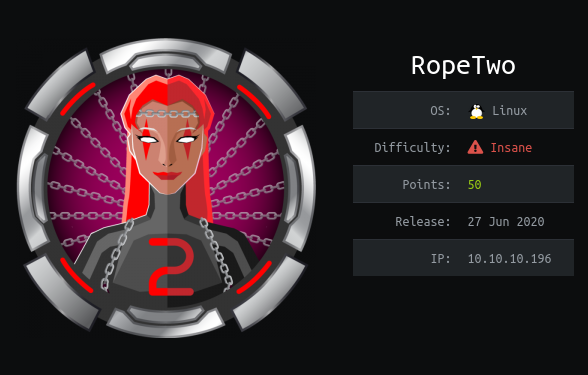
HTB Rope2 Writeup by FizzBuzz101
Rope2 by R4J has been my favorite box on HackTheBox by far. It wasn’t really related to pentesting, but was an immersive exploit dev experience



Comments