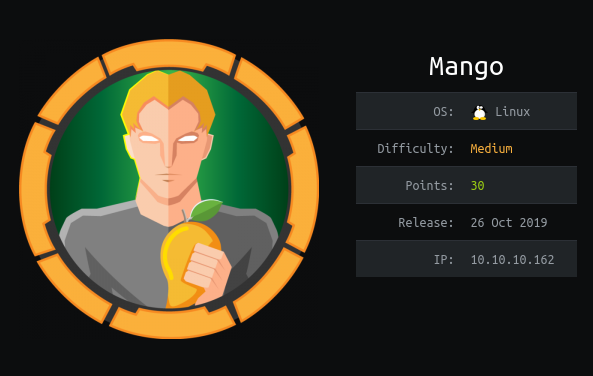
HTB Mango Writeup by plasticuproject
Mango is a medium difficulty box where with basic enumeration and some MongoDB NOSQL Injection we can extract user passwords to log in and get user access. From there we will leverage a classic jjs privilege escalation to get root access and read the root.txt file.